Did you know that data breaches in the healthcare industry cost the company $10.1M on average, according to an IBM report? Data leak in healthcare is a multifactor problem. Today, Acropolium tech experts will tell you how to increase your organization’s security through identity management system modernization, such as an SSO login.
What is Single Sign-On (SSO)? Is it just another IT buzzword or a powerful tool that can simplify enterprise workflows? At Acropolium, we believe it’s the latter, and we’ll show you why.
In this article, our experts explain SSO in simple terms: what an SSO account is, what “sign in with SSO” means for businesses, and the key technologies behind it. We’ll also explore best practices, real-life benefits for industries like healthcare, and the differences between off-the-shelf SSO software and custom enterprise solutions.
What is SSO and why is it important?
It is never too late to invest in your organization’s security improvements. Numbers do not lie – according to Statista, global IT security spending has more than doubled since 2017, hitting $263 billion in 2026 amid escalating cyber risks.
Nowadays, 88% of tech companies worldwide report using SSO, MFA, or a combination of both to safeguard organizational data, up from 75% just a few years ago.
What does SSO mean?
Let us start from the basics and go through the definition of single sign on.
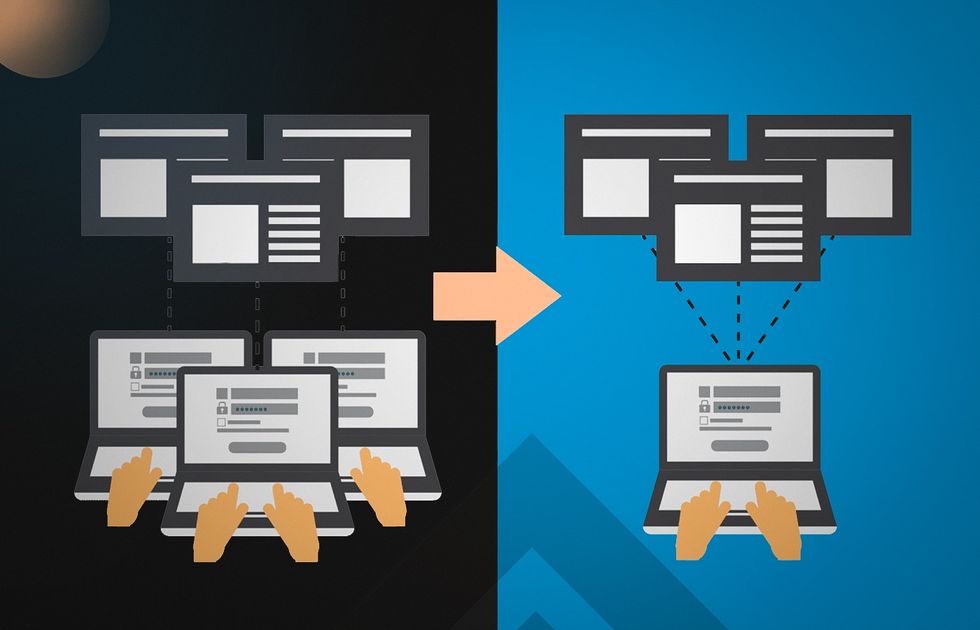
Single sign on ( SSO) is an authentication method that allows users to securely log in using one set of user credentials with multiple applications and sites. It may sound confusing, so let’s briefly describe what is SSO integration and what SSO integration is not.
SSO might seem like a fancy password manager. Yet, that’s far from the truth. Many SSO solutions like Okta, Onelogin, and Duo add an extra layer of security and control to the login process.
An SSO software enables secure authentication for users signing into multiple software systems, online apps, or databases. A single set of credentials that accesses all these apps and services improves cybersecurity hygiene. In turn, it enhances security and makes it easier for you to interact with everyone.

How does single sign on work?
SSO installs a trust relationship between an application (an SSO service provider) or a service and an external service provider (Identity Provider — IdP). SSO authentication methods happen through several steps involving authentication, validation, and communication between the application and a centralized SSO service. When the SSO login meaning is clear, let us proceed to the following crucial aspects of single sign on SSO:
SSO service
SSO services centralize login management. This way, applications don’t have to implement their authentication mechanisms. If an unauthenticated user tries to access an application, the app redirects them to the SSO service. The service authenticates a user and moves them back to their original app. Typically, the service runs on a dedicated SSO policy server.
SSO token
An SSO token is a digital file that consists of user-identifying information, such as username or email address. During the SSO process, systems exchange information they have collected.
Tokens must be digitally signed for the receiver to verify that they come from a trusted source. The digital certificate used for this signature will be exchanged during the initial configuration process.
Identity Provider (IdP)
When users log in with SSO, it verifies their identity with the IdP. Once this verification passes, an SSO can verify user identities with any connected cloud applications.
What Does Sign In With SSO Mean
The login process usually looks like this:
- The application asks the SSO to verify the user’s identity.
- SSO sees that the user still needs to be signed in and prompts to sign in.
- At this point, the user’s browser redirects them to the SSO login page. The latter has fields to enter username and password. After that, they click “Login.” This step requires two-factor authentication, if available.
Now the following things happen:
- SSO sends a request to the SAML IdP used by the user’s company.
- The IdP sends an SSO SAML response confirming the user’s identity.
- SSO sends a SAML assertion to the app the user originally wanted to use.
- The user is redirected back to their application. Now they can use it fully. The whole process took only a few seconds.
SSO Best Practices and Requirements
Several technical concepts of SSO sign in will help you understand its work under the hood. Acropolium team is eager to walk you through it. You can count on us as we provide quality software development services compliant with ISO.
Single sign on best practices include applying the following technologies:
OAuth 2.0
OAuth 2.0 is an authorization protocol that has become a single sign on standard and industry-wide best practice for user authorization. It allows apps access to certain features or user data via API without letting those apps know your password.
However, unlike OAuth 1.0, this access will only last for a short time due to short-lived tokens. Once the access or refresh token expires or gets revoked, the user loses access and needs to start authorization over again. That is why OAuth 2.0 is commonly used in secure single sign on.
Security Access Markup Language (SAML)
SAML is a markup language that allows identity providers (IdP) to talk to service providers to exchange security data. For that, they usually use XML format.
Implementing SAML single sign on for SaaS applications guarantees single sign on security for all your employees.
One of the most common examples is SAML SSO used in Google Workspace. It is configurable and allows workers to reach the organization’s resources using a single set of credentials in different Google apps. Once IT department admins set up single sign on, employees get instant access to SAML-enabled work apps once logged into their Google account.
Federated Identity Management (FIM)
FIM, also known as federated SaaS single sign on, allows setting up SSO by creating a federation of trusted sources. These may include the organization’s vendors or third-party apps.
This method allows using one user identity for several domains, for example, using a company-issued set of creds to access not only Jira and Confluence but also Zoom, Salesforce, or timesheet apps.
OpenID Connect (OIDC)
OIDC is a cross-platform open identity authentication protocol. Built upon OAuth, it has an additional security layer through authentication.
Wondering how single sign on works? In this case, you use one trusted app (like Facebook or Gmail) to log in to another app. In this case of authentication single sign on Facebook or Google serves as IdP and allows you to authenticate the user as an employee of your organization.
It enables SSO secure email login using only your personal account. Proof from a certified IdP allows you to authenticate as an individual associated with your organization to get access.
Key Features of SSO Sign-On Software
End-user UX
Employees may say that their company merely has an SSO integration from the user experience. They will see their company’s single sign on integration by having a unique enterprise login screen.
Cloud-Readiness
Nowadays, employees may sign in to their accounts using desktops, tablets, and mobiles. That is why you should take the usage of cloud applications seriously. If you are already using cloud apps, you have probably satisfied the list of cloud-readiness SSO requirements.
If there is still a way to go with cloud services at your organization, reach out to Acropolium experts for cloud computing consulting services. We are always happy to help.
Centralized Governance
Access tokens are not stored on end users’ devices, and that reduces certain kinds of data breach risks. However, leaks may happen on the upper level, and it would take more work to fix.
Third-Party Integrations
Make sure you trust your vendors and all the software your organization will use. Also, be mindful of prices because many SaaS vendors do not offer SAML support as a basic feature.
It may increase subscription costs up to an extra $5 per user per month, just like with Zoom and Slack.
Single Sign-On Requirements
Before setting up an SSO login, you need to come up with ideas for the following:
- Define the list of apps that you want to include in the company’s SSO plan, and ensure that they support SAML
- Develop regulations in your domain and set up timings for security tokes to live to comply with the rules.
- Accurately calculate the price of SSO implementation. Keep in mind that some vendors provide SSO integration opportunities only in the most expensive enterprise plan.
- Think of additional requirements and obstacles. Combining SSO and MFA (Multi-factor Authentication) is a typical case where complications may occur.
- Educate your staff. After SSO implementation, a password change is necessary. Make sure you communicate it early enough to prevent downtime.
SSO advantages for enterprises.
Some industries successfully adopted an SSO solution long ago because they know why use single sign on. However, some hesitate, still trying to figure out what does SSO stand for in security and other aspects.
SSO Improves User Experience
With one click, users can access all the necessary modules and services, significantly saving time and nerves.
Employees do not need to remember many passwords and to key in logins repeatedly. The SSO secure email login requires you to remember only one password for the entire suite of company resources and with just one pair of credentials — not dozens.
Users can access all the necessary modules and services with one click, significantly saving time and nerves.
Single Sign-On Increases Vitality in Critical Industries
SSO will be incredibly useful in healthcare, finance, or large enterprises. Since many departments and employees need fast and constant access to the same applications/services, seconds of latency will mean the difference between life and death.
SSO Helps With Regulatory Compliance
Depending on the domain, organizations must comply with HIPAA, SOX, and PCI DSS (Payment Card Industry Data Security Standard).
Failure to comply can result in huge fines and other consequences, such as losing the trust of partners, customers, or even employees.
SSO helps you comply with each domain’s specific rules, ensuring adequate access reporting and secure file sharing.
Safety system
A “one-time” login increases the security of high-level company confidential resources. Because the SSO token resides on a central SSO server or database, sensitive login information cannot be cached. Thus, SSO acts as a central point of authentication. This reduces the chance of phishing or malware attacks.
Now when you are sure that SSO would be good for your enterprise, we would like to offer you help adopting this into your company’s identity management system. Not only that, but we also offer a wide range of SaaS services and improvements.
What Industries Need an SSO Solution?

SSO solution is a great deal for industries that suffer from data breaches and spend enormous budgets on cybersecurity to avoid them.
Here is the list of industries that will benefit from security upgrade with SSO:
Finance
Banks and Insurance funds deal with dozens of clients and their bank account information, which turns them into targets for cybercrimes.
Education
Data breaches in educational institutions are hard to notice and fix, which is why data leak prevention is a good strategy here.
Transportation
Logistics and travel companies often require using personal devices, which is why additional security measures are necessary.
Healthcare
Apart from clients’ personal info and bank account details, healthcare institutions deal with sensitive health info and may risk million-dollar fines and reputational losses should it be compromised.
Technology
Even though tech companies, in general, pay attention to their security practices, sometimes they might become vulnerable too, so SSO will help the IT department manage user identities.
No matter which SSO solution you choose, we are always here to help you with device management and single sign-on.
Hospitality
Hospitality workers spend a lot of their time working with booking systems. There is a lot of sensitive information here, from credit card numbers to personal data. It is a good idea to increase system security by implementing SSO login.
Acropolium is not new to security threats, and we encourage you to learn about our experience in the hospitality industry.
In the next section of the article, Acropolium experts will provide insights on the perks that SSO may bring to the healthcare industry.
Benefits of implementing an SSO for the Healthcare Industry

With the telemedicine boom, the percentage of remote and hybrid healthcare workers has risen. There are three reasons for implementing single sign on in healthcare to improve the security of medical services providers and their patients.
According to the statements above, the benefits of a single sign on platform for enterprises include the following.
Saving Time and Effort of Medical Professionals
Healthcare professionals need to access their applications and files from any device, whether in the office or remotely. Unfortunately, the recent BYOD (Bring Your Own Device) trend has resulted in a rising number of cybersecurity incidents and threats.
SSO reduces the time healthcare personnel spend logging into different devices and systems to enhance the clinical workflow, saving time spent on security practices.
According to Gartner, between 20 and 50 percent of all service desk calls, emails, and job tickets deal with password-related issues. This takes valuable time away from other tasks, which may be more important because the IT team must verify the user’s identity before it can accept a change request.
The healthcare SSO requires only one password to remember for all their applications. Just imagine that it helps save up to 11 hours years, which get lost due to previously ineffective security practices.
Better Medical Regulations Сompliance
Healthcare companies must abide by the Healthcare Insurance Portability and Accountability Act (HIPAA) Security Rule to protect their patient’s private data.
Implementing SSO for healthcare helps satisfy HIPAA and other regulatory patient privacy and protection requirements. User authentication and audit controls ensure that only authorized users can access electronic records and audit controls to track access and user activity.
Increasing Employees’ Job Satisfaction Rate
We all sometimes get frustrated with bureaucratic tasks and healthcare workers too. Yet, their core responsibility is to cure patients.
Healthcare single sign on can increase productivity by reducing the time it takes employees to complete tasks like entering passwords, which amplifies the feeling of being overwhelmed. Medical professionals who experience less burnout and greater job satisfaction can provide better patient care.
SSO Software vs SSO Solution

Now that you know why is sso important, it is time to choose the appropriate solution according to the needs of your enterprise.
Enterprise single sign on solutions include existing SSO software and custom SSO solutions. Out-of-box SSO software from trusted single sign on providers such as Okta or KeyCloak may satisfy the needs of enterprises to some extent. Companies that provide single sign on services have developers’ portals where you can find all the info on their integration opportunities.
However, custom single sign-on solutions provide greater customization, including the number of user accounts, identity and recovery token lifetime, enterprise login screen options, and identity management features.
Here you can find a brief comparison of SSO software and SSO solution features.
| SSO Software | Custom SSO Solution | |
|---|---|---|
| Customization | Is possible within SSO software limits and for additional pay | Unlimited |
| Support | SSO provider’s helpdesk | In-house specialist or team |
| Time to set up | Out-of-box solution takes less time to set up | Requires time for development and set up |
| Effort to upgrade | Need to make a feature request, hard to implement | Implementation of your upgrade is guaranteed |
Why choose the SSO solution?

As you see from the article, enterprise SSO solutions are an absolute must for companies that deal with large amounts of data that needs to be secured. SSO solution provides more flexibility than SSO software due to a higher level of customization. What are the benefits of an SSO solution?
It Is Easy to Use For Employees
Users do not need to remember many passwords. The SSO solution requires you to remember only one password for all applications.
It Saves Employees’ Time
SSO can increase productivity by reducing employees’ time on tasks such as entering and recovering passwords.
It Offers Centralized Access Control
Security SSO is built upon platforms that can provide visibility into access rights, login privileges, and user life cycles for companies.
It Stores Credentials Securely
Credentials are stored outside the enterprise, in a cloud or remote SSO platform, and not on the user’s local device. SSO authentication reduces the risk that sensitive data becomes vulnerable.
It Complies With GDPR
Implementing single sign on helps meet regulatory privacy and security requirements. Only authorized users can access electronic records and audit controls to track user access and activities.
Therefore, all large enterprises need SSO services to improve security and reduce the risk of unauthorized access.
Partnership with Acropolium to Protect the App With An SSO
Acropolium brings enthusiastic minds together to make ideas a reality and give you an outstanding scalable solution. The company has developed over 170 small and middle projects and over 50 custom and high-load solutions, including four for Fortune 500 companies.
Acropolium is an experienced vendor of IT solutions. By providing exceptional tech services and dedicated teams, we assist businesses from more than 23 different industries worldwide in disrupting markets and achieving their objectives. Our reputation speaks for us.
We provide a wide range of services: from IT Consulting and end-to-end custom software development to a subscription-based service that covers all everyday needs of a software development project at a monthly fee.
You bring the request to the table, and we bring our expertise to fulfill it. Unlike many companies, Acropolium offers Single Sign-On (SSO) solutions as a part of outsourcing services to help clients securely manage and track project data. We value trust and commitment and believe that choosing the best secure software development practices makes the world a better place. Acropolium is well-versed in serverless solutions, mobile app development, and enterprise web development.
Final Thoughts
Now that you know what is an SSO login and how does SSO work, you can make an informed decision about whether your enterprise needs it. Anyway, it is a trending tool for saving time and budget for any company.
How do you customize single sign-on for your organization? Partner with Acropolium to set up SSO and boost your enterprise security with our subscription-based custom solution.